Development, Operation, and Quality Assurance of Trustworthy Smart IoT Systems
Coordinated by
SINTEF AS
Objective
To unleash the full potential of IoT, realizing the digital society and flourishing innovations in application domains such as eHealth, smart city, intelligent transport systems, and smart manufacturing, it is critical to facilitate the creation and operation of trustworthy Smart IoT Systems. Since smart IoT systems typically operate in a changing and often unpredictable environment, the ability of these systems to continuously evolve and adapt to their new environment is decisive to ensure and increase their trustworthiness, quality and user experience. The DevOps movement advocates a set of software engineering best practices and tools, to ensure Quality of Service whilst continuously evolving complex systems and foster agility, rapid innovation cycles, and ease of use . Therefore, DevOps has been widely adopted in the software industry . However, there is no complete DevOps support for trustworthy smart IoT systems today.
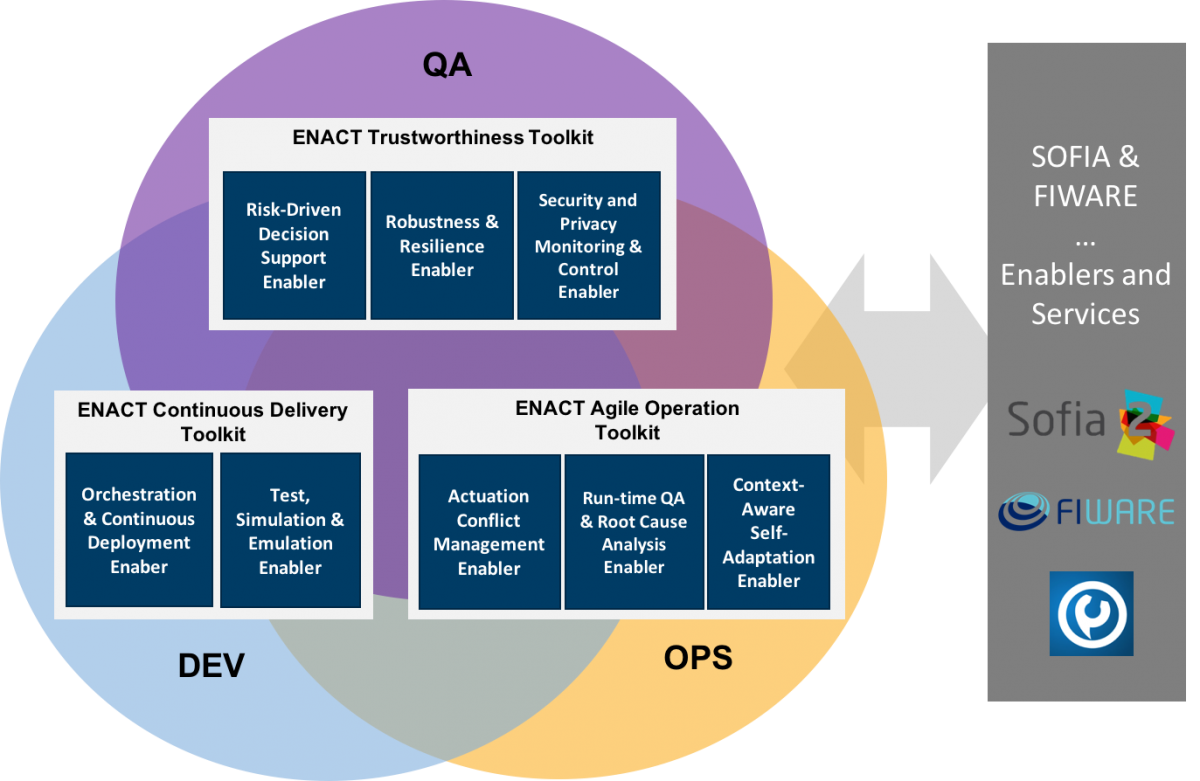
The main technical goal of ENACT is to develop novel IoT platform enablers to:
i) Enable DevOps in the realm of trustworthy smart IoT systems, and enrich it with novel concepts for end-to-end security and privacy, resilience and robustness strengthening trustworthiness, taking into account the challenges related to “collaborative” actuation and actuation conflicts.
ii) Facilitate the smooth integration of these to leverage DevOps for existing and new IoT platforms and approaches (e.g. FIWARE, SOFIA, and TelluCloud).
This will be accomplished by evolving current DevOps methods and techniques to support the agile development and operation of smart IoT systems, and provide a set of novel mechanisms to ensure quality assurance and trustworthiness, such as actuation conflict handling, continuous testing and delivery across IoT, edge and cloud spaces and end to end security and privacy management. Through this ENACT will provide a DevOps framework for smart IoT Systems
Other projects
ELECTRON – rEsilient and seLf-healed EleCTRical pOwer NanogridELECTRON –
ELECTRON - rEsilient and seLf-healed EleCTRical pOwer Nanogrid Objective ELECTRON is EU H2020 SU-DS04-2018-2020 funded research project that aims at delivering a new-generation EPES platform, capable of empowering the resilience of energy systems against cyber,...
ERATOSTHENES – IoT Trust and Identity Management Framework
ERATOSTHENES - IoT Trust and Identity Management Framework Objective The growth of IoT deployment and the contemporary advancements of network technologies will lead to even higher penetration of IoT devices in every aspect of human life. This will undoubtedly...
ENTRUST – Ensuring Secure & Safe Connected Medical Devicea Design with Zero Trust Principles
ENTRUST - Ensuring Secure & Safe Connected Medical Devicea Design with Zero Trust Principles Objective ENTRUST sits at the forefront of digital transformation for the Healthcare domain as it moves into the next generation of Connected Medical Devices, where...
CERTIFY – aCtive sEcurity foR connecTed devIces liFecYcles
CERTIFY - aCtive sEcurity foR connecTed devIces liFecYcles Objective CERTIFY has SMART (Specific, Measurable, Achievable, Realistic and Timely) Specific Objectives. Cybersecurity awareness for IoT-enabled environments through a multi-stakeholder sharing of...
NebulOuS – Cloud Continuum Optimization
NebulOuS - Cloud Continuum Optimization ObjectiveNebulOuS will transparently manage all the layers of the cloud continuum stack, in an equivalent manner to an OS managing the available computing capacity to facilitate an adaptive application hosting...
NetZeroCities – Towards climate neutral European Cities
NetZeroCities - Towards climate neutral European Cities ObjectiveNetZeroCities is part of the Horizon 2020 Research and Innovation Programme in support of European Union’s Green Deal. NetZeroCities has been designed to help cities overcome the current...